Is there an iOS 10.2.1 jailbreak or iOS 10.3 jailbreak right around the corner? The problem with movement within the jailbreak community is often a long period of silence followed by a sudden surge in activity by several key members, followed by a release either in beta or public.
Case in point is the long wait we had for Luca Todesco’s Mach_Portal+Yalu iOS 10.1.1 jailbreak, which was followed by another one, the semi-tethered Yalu102 iOS 10.2 jailbreak for 64-bit devices other than iPhone 7.
The first of these was based on Project Zero exploits from Google, as published by Ian Beer. Unfortunately, Apple patched that exploit when it pushed iOS 10.2, which prompted the yalu102. But that one left iPhone 7 users out in the cold.
As such, what’s the status on an iOS 10.2.1 or iOS 10.3 jailbreak? iOS 10.2.1 is still being signed by Apple, so we highly recommend that you save your SHSH2 blobs before Apple releases iOS 10.3, which could be in a matter of a couple of weeks.
Here’s how to do that: Save your SHSH2 Blobs
So, now, we’re in a situation where Todesco has made it know that he is not going to be working on public jailbreaks any more. And with no iOS 10.2.1 jailbreak or iOS 10.3 exploits in public view, as far as we know, it’s up to Pangu or TaiG to use the exploits they are supposedly sitting on for both iOS 10.2.1 and iOS 10.3, and release a public jailbreak for either of those OS versions.
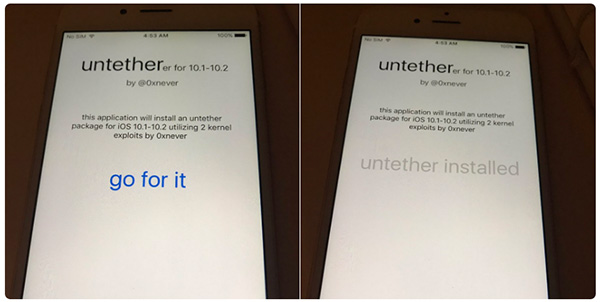
On the plus side, we also know that an untethered iOS 10.2 jailbreak (Yalu102) is potentially in the works. It all started about a day ago on Twitter, where a developer by the name of Lang Shi stated: “Btw my “untetherer” tool for iOS 10.x is almost ready, turn your semi-tethered Yalu into fully untethered with 1 tap!”
Btw my “untetherer” tool for iOS 10.x is almost ready, turn your semi-tethered Yalu into fully untethered with 1 tap! pic.twitter.com/yW7PCnkHbH
— Lang Shi (@0xnever) March 16, 2017
So we can see the activity in the jailbreak community is picking up after a gap, which means something is cooking. Lang Shi had earlier said that he had found “2 new kernel UAF bugs in iOS 10.3b7,” which initially sparked off discussions.
Some validation came from the two images he posted along with the note on the “untethered tool.”
Lang Shi followed that up with another tweet which indicated that one of the kernel exploits used is still present on the latest beta for iOS 10.3, which is beta 7. He added that the tool will work for iPhone 7 users on jailbroken iOS 10.1 devices using the mach_portal tool. That could also indicate an iOS 10.3 jailbreak to follow at a later date.
While that sounds like great news, any jailbreak is only legit once it’s released, either in beta or as a public release. We’re optimistic about this one, but we’ll still have to wait and see.
On another note, we would like to warn new jailbreakers that any type of jailbreaking can void your warranty. So, if you have a new device, it’s not recommended. Either way, jailbreaking must be done at your own risk because of the variables involved. We cannot take any responsibility for anything that happens during the process.
Thanks for reading our work! Please bookmark 1redDrop.com to keep tabs on the hottest, most happening tech and business news from around the world. On Apple News, please favorite the 1redDrop channel to get us in your news feed.



