In the battle of browsers, dumb luck sometimes helps gain an edge. Google Chrome, Opera and Firefox are susceptible to attacks because of a newly discovered vulnerability, but the same vulnerability isn’t found on Microsoft Edge, Internet Explorer and Vivaldi because of a specific reason.
The vulnerability itself was detected by a Chinese security expert in the form of a phishing attack that used this flaw in Google Chrome and other affected browsers. Apparently, the bad actors trick users into entering their details into sites that look genuine – Apple.com, eBay.com and so on. The catch is this: even though the URL looks legit, it’s actually completely different from what it should be.
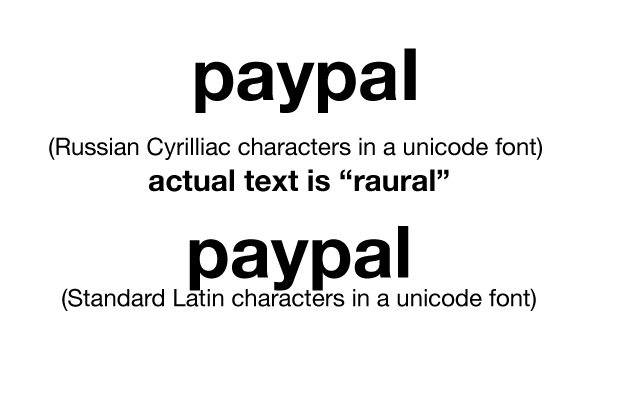
By using a new version of an old method called IDN homograph that was first unearthed more than 15 years ago in 2001, attackers are able to mask the URL and make it look authentic.
For example, one attack uses the URL ‘xn-80ak6aa92e.com’, which is displayed on Google Chrome as https://www.Apple.com – note that even the https is present, although this security certificate is not signed by Symantec, the certificate issuer that Apple uses, but another – Comodo.
You can see how dangerous this type of attack might be. Unsuspecting users will try and log in or put in some other information thinking that it’s the real website, and the bad actors gather this often personal data for other nefarious purposes.
Why are Microsoft Edge, IE and Vivaldi immune to this? To be precise, they aren’t. But the big difference with these browsers is that they display the URL as-is, not as the purported one. For example, on IE or Microsoft Edge on a Windows 10 machine will show xn-80ak6aa92e.com as exactly that – xn-80ak6aa92e.com. That sends a warning signal to the user that this site isn’t what it is pretending to be.
Google Chrome appears to have patched this vulnerability on the dev version of Google Chrome 59, but it will only make its appearance to the general public along with Google Chrome 58, which drops later this month.
That means there’s a big window of attack open to potential bad actors using this flaw to phish for personal, sensitive data from users. It’s not a practical solution to stop all your browsing activity just because of a flaw. So, if you’re on Windows 10 using Edge or IE, you’re safe – as long as you watch those URLs.
If you’re on a non-Windows device, or if you’re on Windows 10 but use Google Chrome, switch over to IE, Microsoft Edge or Vivaldi until Google Chrome 58 is released to the stable channel. Apple users are advised to switch to Safari temporarily.
This is not a kudos for Microsoft Edge or a criticism of Google Chrome. The reason that the Windows 10 default browser is not easily fooled by this technique is that it simply does not display the alternate characters that the attacker uses. It will simply show you exactly what the attacker is trying to do. This does give you the opportunity navigate away from the page, but you have to manually spot it. That’s why it’s dumb luck.
Thanks for reading our work! If you enjoyed it or found value, please share it using the social media share buttons on this page. If you have something to tell us, there’s a comments section right below, or you can contact@1redDrop.com us.
Source: HiTechGazette