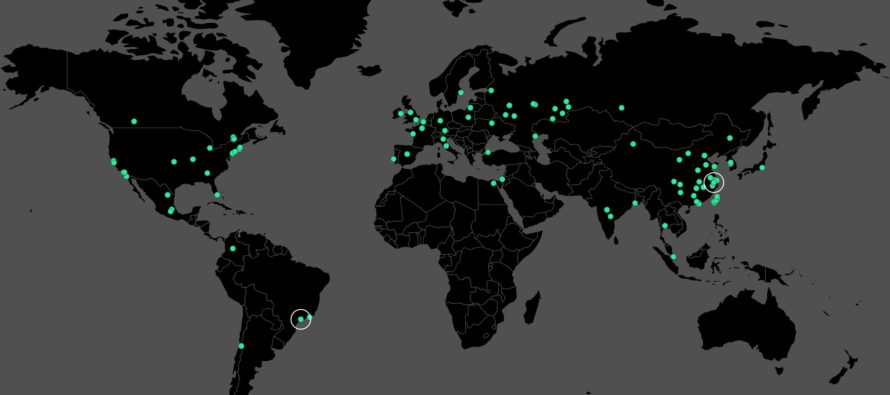
Earlier this week, many of the world’s systems across dozens of countries were crippled by what is possibly the most prolific and fast-spreading ransomware attack in recent times. Healthcare providers, businesses and consumers alike were hit by the WannaCrypt software across the globe, and the attacks are not stopping. Microsoft has issued a customer guidance for the WannaCrypt attacks.
In March, Microsoft patched this particular vulnerability on which the exploit behind these attacks are based, but several organizations around the world did not deploy the security update: Microsoft Security Bulletin MS17-010. Microsoft is now urging any organization or consumer that has not applied this security update to do so now.
In addition, the company released another update two days ago, and this detects the attack as Ransom:Win32/WannaCrypt on all machines that have Windows Defender. Microsoft is also advising companies and consumers to keep their anti-malware software up to date, and to confirm with their providers that they are, in fact, protected from this attack.
Microsoft also clarified that customers running Windows 10 were not targeted by the attack, and the company has also pushed the new security update to all Windows XP, Windows 8 and Windows Server 2003 customers.
For all other versions – Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8.1, Windows Server 2012, Windows 10, Windows Server 2012 R2, Windows Server 2016 – Microsoft asks them to apply the MS17-010 update if they haven’t enabled autoupdates on their systems.
Microsoft is being very clear about one thing: if a particular Windows version is not currently supported, they will not get a further security update. The exception that Microsoft made for Windows XP, Windows 8 and Windows Server 2003 customers is based on this decision by Microsoft:
“Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download.
This decision was made based on an assessment of this situation, with the principle of protecting our customer ecosystem overall, firmly in mind.”
If you read between the lines, and count the fact that Windows 10 devices were not targeted, the message is pretty clear: Upgrade to Windows 10 or struggle with getting security protection moving forward.
Whether or not this particular WannaCrypt attack will “encourage” users to move to Windows 10 is something we’ll have to wait and see when the install base report for May comes out next month, but it’s likely that those that have been hit may seriously consider upgrading.
Based on which version of Windows or Windows Server version you are using, you can apply the relevant security patches using these links below, provided by Microsoft:
Download English language security updates: Windows Server 2003 SP2 x64, Windows Server 2003 SP2 x86, Windows XP SP2 x64, Windows XP SP3 x86, Windows XP Embedded SP3 x86, Windows 8 x86, Windows 8 x64
Download localized language security updates: Windows Server 2003 SP2 x64, Windows Server 2003 SP2 x86, Windows XP SP2 x64, Windows XP SP3 x86, Windows XP Embedded SP3 x86, Windows 8 x86, Windows 8 x64
General information on ransomware: https://www.microsoft.com/en-us/security/portal/mmpc/shared/ransomware.aspx
MS17-010 Security Update: https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
Thanks for visiting! Would you do us a favor? If you think it’s worth a few seconds, please like our Facebook page and follow us on Twitter. It would mean a lot to us. Thank you.
Source: Microsoft