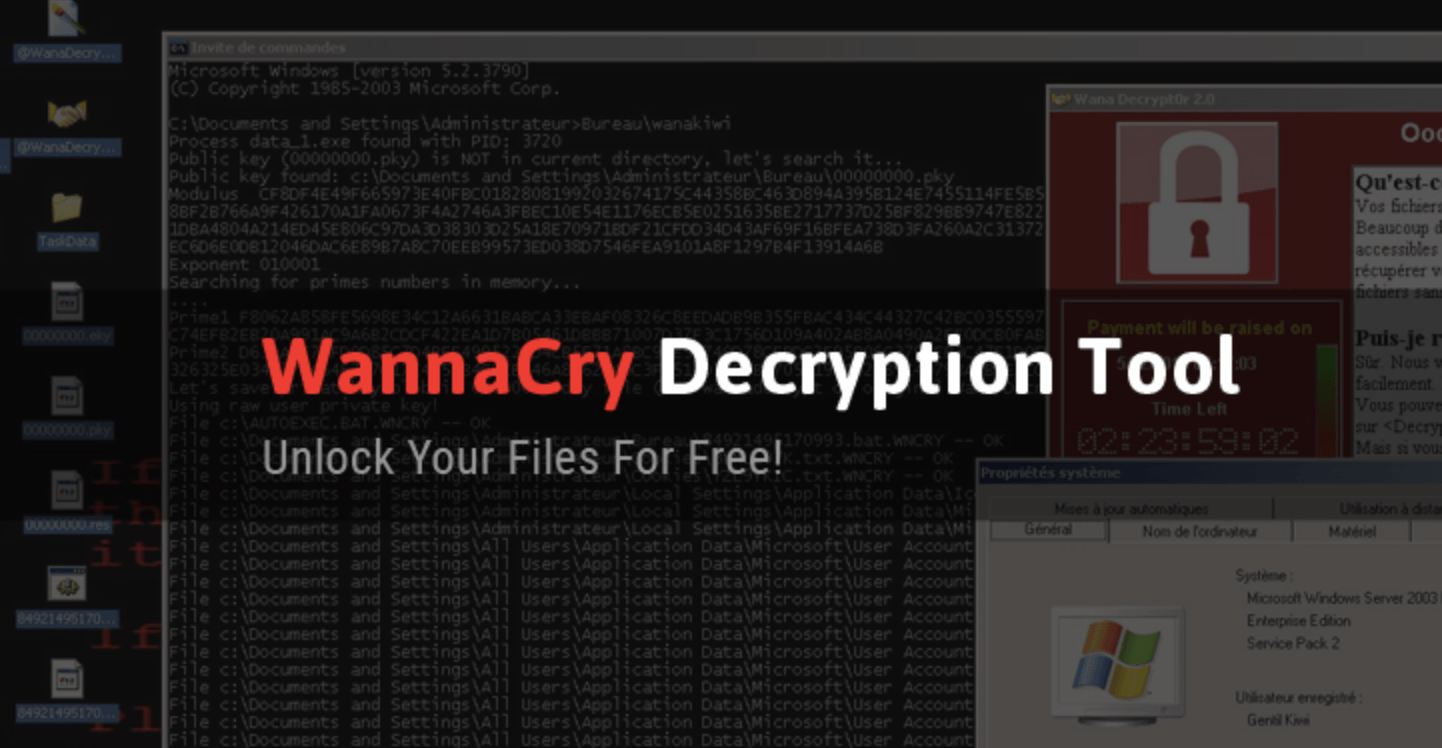
If you’ve been the victim of a WannaCry ransomware attack, DO NOT PAY any money to the attackers. A french security researcher from Quarkslab, Adrien Guinet, has figured out the critical pieces of information that allow the victim to retrieve the encryption keys that are used by the WannaCry malware. The tool, actually developed by another security researcher, works on Windows XP, Windows 7, Windows Vista, Windows Server 2003 and 2008 operating systems, and uses the findings of Guinet in a free decryption tool called WanaKiwi.
Understanding How WannaCry Ransomware Works
To understand the mitigation process, we need to understand how the encryption is done in the first place. The WannaCry ransomware works by generating two “keys”, a private one and a public one. It relies on prime numbers for this. The public key is for encrypting, and the private key is for decrypting the victim’s data and files.
Now, in order to prevent the victim from accessing the private key for the decryption part, WannaCry deletes the key from the local system. That means the victim has to pay to get the key from the attackers.
But Guinet has found a flaw:
WannaCry “does not erase the prime numbers from memory before freeing the associated memory.”
Based on this flaw, Guinet has been able to develop something he calls WannaKey. But the problem is, Guinet’s tool can only pull out the prime numbers used to generate the encryption and decryption keys in the first place, not generate the decryption key required to unlock the files in question. And it only works on Windows XP.
However, using Guinet’s findings, Benjamin Delpy, another security researcher, has developed a tool called WanaKiwi.
WanaKiwi is Free, and It Could Work for You
The tool is very simple to use, and you don’t even need to know how to get it to work. Simply download the tool from GitHub for free, and run it on your affected Windows PC on the command line (cmd).
The tool works on all the Windows PC and Server versions mentioned at the beginning of this article.
Download the Free WanaKiwi Tool and Try to Decrypt your Encrypted Files
To see how this tool works, you can watch some demos from Matt Suiche of Comae Technologies, a security firm.
Unfortunately, there are some dependencies that could prevent the WanaKiwi tool from working. For example, it won’t work if the affected computer has been rebooted after the attack. It also won’t work if the associated memory has not been allocated and erased by another process.
Still, there’s a good chance that it will work on your system as long as you’ve done nothing since the attack. It also depends on the highly technical factor called “luck”, or so the developer warns.
But if it can help decrypt your valuable files, then anything is worth a try as long as it doesn’t cost you $300 in bitcoins.
Thanks for visiting! Would you do us a favor? If you think it’s worth a few seconds, please like our Facebook page and follow us on Twitter. It would mean a lot to us. Thank you.