AppLocker on Windows 10 is an often-underrated security layer that addresses what is now coming to the forefront of enterprise security – threats from ransomware and other malware. First introduced with Windows 7/Server 2008 R2 as an update from the Software Restriction Policies feature (XP/2003), it allows non-admins to be restricted to a certain set of applications.
How Can AppLocker Protect Networks from Ransomware Attacks?
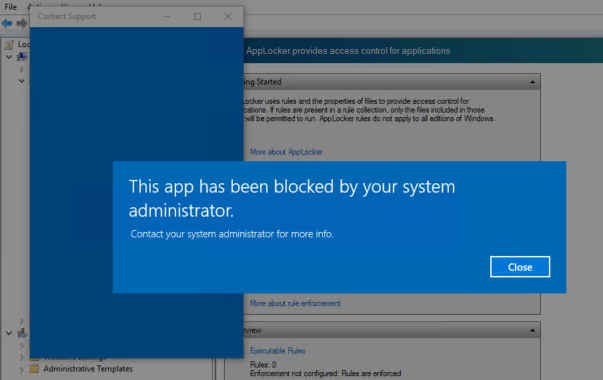
AppLocker can be used to predefine what types of apps can be run by which users. Specifically, it controls apps such as executable .exe and .com files, .js, .ps1, .vbs, .cmd, and .bat scripts, .msi and .msp Windows Installer files and DLL files like .dll and .ocx.
When the threat of unwanted software is high, AppLocker can be used to reduce that threat to a great degree.
Specific to ransomware, the job of AppLocker is to prevent software from a non-admin’s writable workspace from being executed. And the reason that’s required is that the Windows file system, NTFS, grants read/write permission to all non-admin users, and some “authenticated users” (also non-admins) even get read/write permissions to %WinDir%/Temp.
While AppLocker doesn’t change NTFS permissions; what it does is to prevent non-admins from saving files to an executable location. In doing this, AppLocker reduces the surface area for potential malware attacks, including ransomware.
Earlier this month, the United States Computer Emergency Readiness Team, or US-CERT, issued Alert (TA17-163A), which recommends application whitelisting (AWL) in order to “detect and prevent attempted execution of malware uploaded by adversaries.”
The alert specifically mentions AWL tools such as AppLocker to implement application or application directory whitelisting.
One important thing to remember is that the default rules in AppLocker are only the starting point. To be truly effective, admins need to know which folders non-admins have both execute and write permissions on.
This is why the initial planning stage for rolling out AppLocker delivery is critical. New applications will naturally create new folders and files, and admins have to be on top of these changes.
One way to do this is by creating scripts to read non-admin system folders to identify which locations they have execution capabilities in. The rule set in AppLocker should necessarily depend on on where these writable and executable folders are. There are also other tools created by independent security researchers that you can use, such as AppLocker Bypass Checker. You can also use accesschk from Windows Sysinternals to find user-writable folders.
The point is, the tools are there, but they need to be used effectively.
AppLocker is merely one layer in a series that protects your systems, but it is a critical one that needs to be addressed sooner rather than later. Too many admins merely use the default rules and assume that everything is taken care of, and that’s where the real danger lies.
Windows 10 may be far more resilient to attacks from ransomware and malware, but assuming that Microsoft is going to do all the work is possibly the biggest mistake a SysAdmin can make.
Note: Windows 10 is not the only version where AppLocker can be configured and enforced, but other versions may have some restrictions. Please see the table below, and the additional resource link below that:
| Version | Can be configured | Can be enforced | Available rules | Notes |
|---|---|---|---|---|
| Windows 10 | Yes | Yes | Packaged apps Executable Windows Installer Script DLL |
You can use the AppLocker CSP to configure AppLocker policies on any edition of Windows 10. You can only manage AppLocker with Group Policy on devices running Windows 10 Enterprise, Windows 10 Education, and Windows Server 2016. |
| Windows Server 2016 Windows Server 2012 R2 Windows Server 2012 |
Yes | Yes | Packaged apps Executable Windows Installer Script DLL |
|
| Windows 8.1 | Yes | Yes | Packaged apps Executable Windows Installer Script DLL |
Only the Enterprise edition supports AppLocker |
| Windows RT 8.1 | No | No | N/A | |
| Windows 8 Pro | No | No | N/A | |
| Windows 8 Enterprise | Yes | Yes | Packaged apps Executable Windows Installer Script DLL |
|
| Windows RT | No | No | N/A | |
| Windows Server 2008 R2 Standard | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows Server 2008 R2 Enterprise | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows Server 2008 R2 Datacenter | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows Server 2008 R2 for Itanium-Based Systems | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows 7 Ultimate | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows 7 Enterprise | Yes | Yes | Executable Windows Installer Script DLL |
Packaged app rules will not be enforced. |
| Windows 7 Professional | Yes | No | Executable Windows Installer Script DLL |
No AppLocker rules are enforced. |
Additional Resource: Requirements to Use AppLocker
Thanks for visiting! Would you do us a favor? If you think it’s worth a few seconds, please like our Facebook page and follow us on Twitter. It would mean a lot to us. Thank you.