Though there’s not been much movement on Nintendo Switch availability in recent weeks, inventory has been randomly appearing and various retail stores and online portals in the UK. Apparently, there are some units available at Amazon.co.uk (very few when we checked), Toys R Us UK stores and at Smyths.
North America doesn’t seem to be having much luck with Nintendo Switch availability, with sporadic appearances on Amazon.com and other sites.
Meanwhile, despite the bottleneck in getting Nintendo Switch to retailers across the world, the company is asking developers to help find security vulnerabilities on Nintendo Switch and Nintendo 3DS platforms.
In a new posting on HackerOne, Nintendo has launched a bug bounty that rewards security researchers between $100 and $20,000 depending on the severity of the flaw.
This is a listing of vulnerabilities that Nintendo wants researchers to find on the Nintendo Switch gaming system platform:
- System vulnerabilities regarding Nintendo Switch
- Privilege escalation from userland
- Kernel takeover
- ARM® TrustZone® takeover
- Vulnerabilities regarding Nintendo-published applications for Nintendo Switch
- Userland takeover
- System vulnerabilities regarding the Nintendo 3DS family of systems
- Privilege escalation on ARM® ARM11™ userland
- ARM11 kernel takeover
- ARM® ARM9™ userland takeover
- ARM9 kernel takeover
- Vulnerabilities regarding Nintendo-published applications for the Nintendo 3DS family of systems
- ARM11 userland takeover that doesn’t require other hacks or tools (“secondary” exploits would be those that require other hacks or tools to be effective; those would be out of scope for this program)
- Hardware vulnerabilities regarding either the Nintendo Switch system or the Nintendo 3DS™ family of systems
- Low-cost cloning
- Security key detection via information leaks
They’re also trying to prevent certain activities, as follows:
- Piracy, including:
- Game application dumping
- Copied game application execution
- Cheating, including:
- Game application modification
- Save data modification
- Dissemination of inappropriate content to children
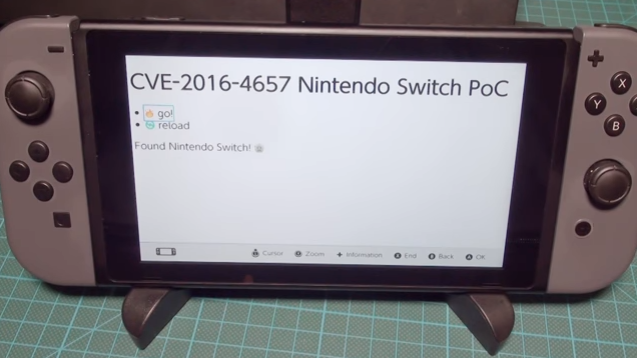
Nintendo clearly says that it will decide what vulnerabilities to patch, or whether it is dependent on an actively used exploit being available in the wild and so on. However, they will treat a vulnerability as being “high quality” if a PoC or, especially, a fully functional exploit code is made available.
Reporters are given three weeks to provide the PoC or exploit code after they initially report the flaw. Unlike a lot of tech companies that often reveal the amount of the bug bounty for specific vulnerabilities, Nintendo categorically states that it will not disclose that information to the public.
As for Nintendo Switch availability, it’s still a touch and go situation, and we’ve provided as much information as possible on the options available. But it boils down to your luck in the end. Hopefully, with more games coming this Summer, Nintendo is looking at upping its shipments so at least a portion of the tremendous demand that’s been generated in the past five weeks or so since its launch can be satisfied.
Thanks for reading our work! If you enjoyed it or found value, please share it using the social media share buttons on this page. If you have something to tell us, there’s a comments section right below, or you can contact@1redDrop.com us.